Robust Web and API Protection
Web Application & API Protection (waap)
Elevating Cybersecurity Standards with Comprehensive Web and API Protection in an Increasingly Digitalized Global Landscape
Advanced WAAP Defense
Security for Web Applications and APIs in an Increasingly Vulnerable Digital Landscape
Web applications and APIs are accessible via the public Internet and provide access to sensitive data, making them a main target for attackers. Traditional security solutions cannot effectively protect these applications, making WAAP a must. Protect your applications and APIs against threats and fraud, help ensure availability and compliance.
WAAP anywhere, for less
Get proven, comprehensive protection of applications and APIs from a single vendor while potentially saving 50%–70% over competing solutions.
Simplify Operations
Reduce the number of vendors you work with to protect your apps; leverage integrations with Google Cloud tools for consolidated management and visibility.
All Purpouse
Anti-DDoS, anti-bot, WAF, and API protection help you protect against new and existing threats while helping you keep your apps and APIs compliant and continuously available.
Robust Security
Fortify your digital presence against existing and emerging threats with our cutting-edge Web Application and API Protection solutions, ensuring unparalleled cybersecurity.
Edgewatch Bastion WAAP key features
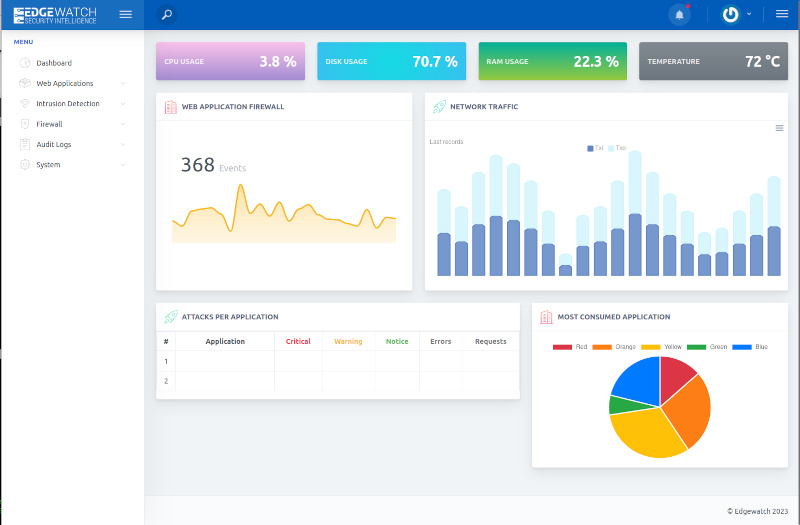
Edgewatch Bastion, a Next-Generation Web Application Firewall (Next-Gen WAF), offers unparalleled protection and monitoring for web applications. It operates at the crucial application layer, where web applications are most vulnerable.
Unlike traditional WAFs, Edgewatch Bastion utilizes advanced behavioral analysis and artificial intelligence (AI) to identify and thwart attacks. This innovative approach allows it to effectively block not just known threats but also emerging and sophisticated attacks, without relying solely on pre-defined attack patterns and manual security rules. By incorporating AI, Edgewatch Bastion adapts to evolving threats, ensuring real-time protection and maintaining the integrity and availability of web applications. This makes it an indispensable tool in the modern cybersecurity landscape, where the nature and frequency of attacks are constantly changing.
API Throtling
Advanced rate limiting safeguards against abusive activity at the application level which adversely influences website and API performance.
Basic DDoS Protection
Basic Distributed Denial-of-Service (DDoS) Protection that safeguards against DDoS attacks targeted at applications, APIs and microservices, at the application and network layers. Able to scale up to defend against massive-scale attacks.
RASP
Runtime Application Self-Protection (RASP) embedded in the application runtime domain, this offers real-time attack defense for APIs and web applications.
Bot Protection
Malicious bot protection that isolates and stops attacks from suspicious bots and opportunistic scans while permitting safe bot traffic to reach the application.
Takeover protection
Safeguards against cybercriminals using compromised credentials from data dumps and password lists. Detects unauthorized access to customer accounts via authentication APIs or an application’s customer-facing authentication process.
API Protection
Protection for microservices and APIs places security within the microservice, application, or serverless function to produce a context and data-aware micro perimeter around all individual services.